What is WebRTC leak?
This article explains what WebRTC is and how the WebRTC leak that may expose your real IP address while connected to VPN, proxy, or TOR.
What is WebRTC?
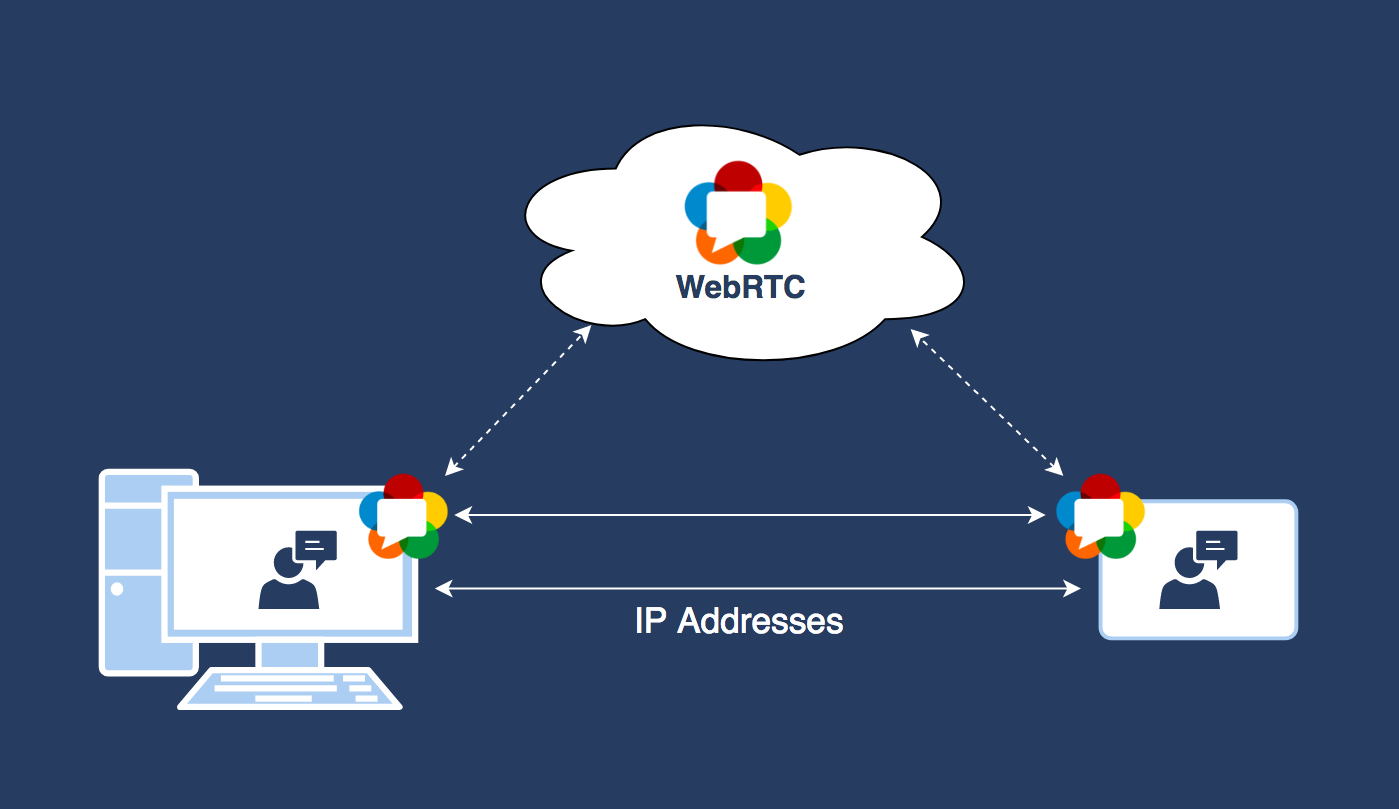
WebRTC stands for Web Real-Time Communication and is a set of standard technologies that enables web browsers to communicate directly with each other, without needing an intermediate server. WebRTC has the benefits of less lag for web applications like live streaming, file transfer, and video chat, and also enables faster speeds.
WebRTC enables Real-Time Communications capabilities in mobile applications and web browsers by using JavaScript to enable applications to run in browsers without having to use external plugins.
An essential aspect of the WebRTC technology is that it relies on external servers. You may read about STUN servers and TURN servers here.
WebRTC APIs are supported by most browsers and is often enabled by default.
What is the WebRTC leak?
With WebRTC, devices can talk to each other directly (via STUN/TURN servers), but to do so, the devices need to know each other’s real IP address. This could however also permit third-party websites to use the WebRTC in a browser to detect a device’s real IP address, and this can, in turn, be used to identify the user of the device. This vulnerability is known as a WebRTC leak.
YOUR PUBLIC IP ADDRESS IS: 216.73.216.101
Whenever a device’s public IP address can be determined from the outside, it threatens the user’s privacy. WebRTC leaks are however not well known, and they can, therefore, be overlooked easily. Not all VPN or proxy providers will have security in place to protect against WebRTC leaks.
Which browsers are affected?
The Chrome, Firefox, Microsoft Edge and Opera browsers are most vulnerable to WebRTC leaks, simply because these browsers enable WebRTC by default.
How to check if you are exposed
A public IP address is highly specific to a user as a form of the user’s identity on the internet. When VPNs or other hide IP tools are used, websites that are being browsed will not see the user’s public IP address, but the VPN server’s public IP will be revealed, thereby protected the user’s identity.
If the WebRTC functions are, however, able to detect the real public IP address when a VPN is being used, rather than the public IP of the VPN server, third parties will still be able to use it to identify the user.
There are a number of utilities available on the internet that will allow you to check if you have a WebRTC. When using such a tool (like our WebRTC leak test), the private IP address it shows is of no concern as these are not unique and can’t be used to identify you. The public IP address is what is important in this case.
If you’re not using a VPN, chances are high that you are exposing some private information to third parties. If a public IP is displayed in the test results of the WebRTC leak detection utility you use, you may have a privacy leak.
If you are using a VPN and the WebRTC leak tool still shows that there might be a leak, the following leak test can be performed to be sure:
- Disconnect from the VPN and open the WebRTC leak tool page in a new window or tab.
- Write down the public IP addresses that are displayed in the utility.
- Close the WebRTC leak tool page.
- Connect to your VPN and open the WebRTC leak tool page again.
- If the same public IP addresses you wrote down in Step 2 are still displayed, you have a privacy leak.
If you are using a VPN (OpenVPN or other VPN protocols) and the WebRTC leak tool tells you there is no leak, your public IP address is safe and you don’t need to worry.
How to protect yourself from WebRTC leaks
It is important to understand that WebRTC is used by certain websites to provide audio and video communication capabilities. Thus, by disabling WebRTC, some of these websites may not work anymore!
You may protect yourself from WebRTC request leaks by:
- Disabling WebRTC in your browser (check the instructions below).
- Using a VPN, proxy or TOR solution that hides your IP address and does not leak WebRTC requests (check the Hide IP page). Some of them have the WebRTC leak protection enabled by default.
How to disable WebRTC in various Web browsers
Important note! By disabling the WebRTC functions, the performance of applications that use WebRTC for audio/video or real-time data communication may be affected!
How to disable WebRTC in Google Chrome
The Google Chrome browser does not allow you to access WebRTC settings directly. However, you may install a browser extension like the WebRTC Leak Prevent Chrome extension to disable WebRTC.
- Access the WebRTC Leak Prevent's configuration page (View > Show Extensions > WebRTC Leak Prevent > Options).
- Select Disable non-proxied UDP (force proxy) from the drop-down menu.
- Click Apply settings button.
- Perform the WebRTC leak test.
Another excellent Chrome extension is the WebRTC Network Limiter. It requires WebRTC traffic to go through proxy servers as configured in Chrome.
How to disable WebRTC in Mozilla Firefox
- In the browser address bar type about:config.
- Click on the I accept the risk! button.
- Find the media.peerconnection.enabled option.
- Set the value to false.
- Perform the WebRTC IP leak test.
How to disable WebRTC in Opera
To implement the WebRTC block on Opera, you need to install and set up the WebRTC Leak Prevent Opera extension:
- Access the extension's configuration page (View > Show Extensions > WebRTC Leak Prevent > Options).
- Select Disable non-proxied UDP (force proxy) from the drop-down menu.
- Click Apply settings button.
- Perform the WebRTC leak test to check that WebRTC is completely disabled.
How to block WebRTC leaks in Microsoft Edge
There is no way to completely disable WebRTC in Microsoft Edge completely. However, you can set your browser to hide your local IP address:
- Type about:flags into the address bar.
- Check the option Hide my local IP address over WebRTC connections.
How to protect yourself from WebRTC leaks in Safari
You probably won’t have to disable WebRTC in Safari. The permissions model of Safari is stricter than that implemented in most browsers. IP addresses are not made available to websites by default, except the one used to access a site. It should therefore not be necessary to take any additional actions to prevent WebRTC leaks in Safari. It should, however, be noted that if any specific site permission is granted to use video or audio capture, the IPs might be exposed.
Summary
WebRTC can be very useful. If you are however worried about online anonymity and privacy, you should realize that your real IP could be exposed. Remember that any website that is accessed can use WebRTC, possibly putting your online privacy at risk.
It is important to understand is that a WebRTC IP leak is a web browser vulnerability and not that of a VPN or a proxy.
